
AI workflow platforms are essential for securely managing sensitive data in industries like finance, healthcare, and government. This article reviews five leading platforms - Prompts.ai, Workato, n8n, Stack AI, and Vellum AI - based on their security features, compliance certifications, governance tools, and cost efficiency. Key highlights include:
Each platform balances security, compliance, and operational needs, making them suitable for various organizational requirements. Below is a quick comparison:
| Platform | Key Features | Compliance Certifications | Starting Cost |
|---|---|---|---|
| Prompts.ai | AI usage monitoring, audit tools | SOC 2, GDPR | Free for up to 5 apps |
| Workato | Enterprise-grade encryption, RBAC | PCI DSS 4.0, ISO 27001, SOC 1/2/3 | Premium pricing |
| n8n | Self-hosting, FIPS-compliant storage | SOC 2, GDPR | $20/month |
| Stack AI | On-premise, PII masking | SOC 2, HIPAA (ISO 27001 pending) | Custom pricing |
| Vellum AI | HMAC signatures, role-based access | SOC 2, HIPAA | $25/month |
Choose a platform that aligns with your security priorities, compliance needs, and budget.
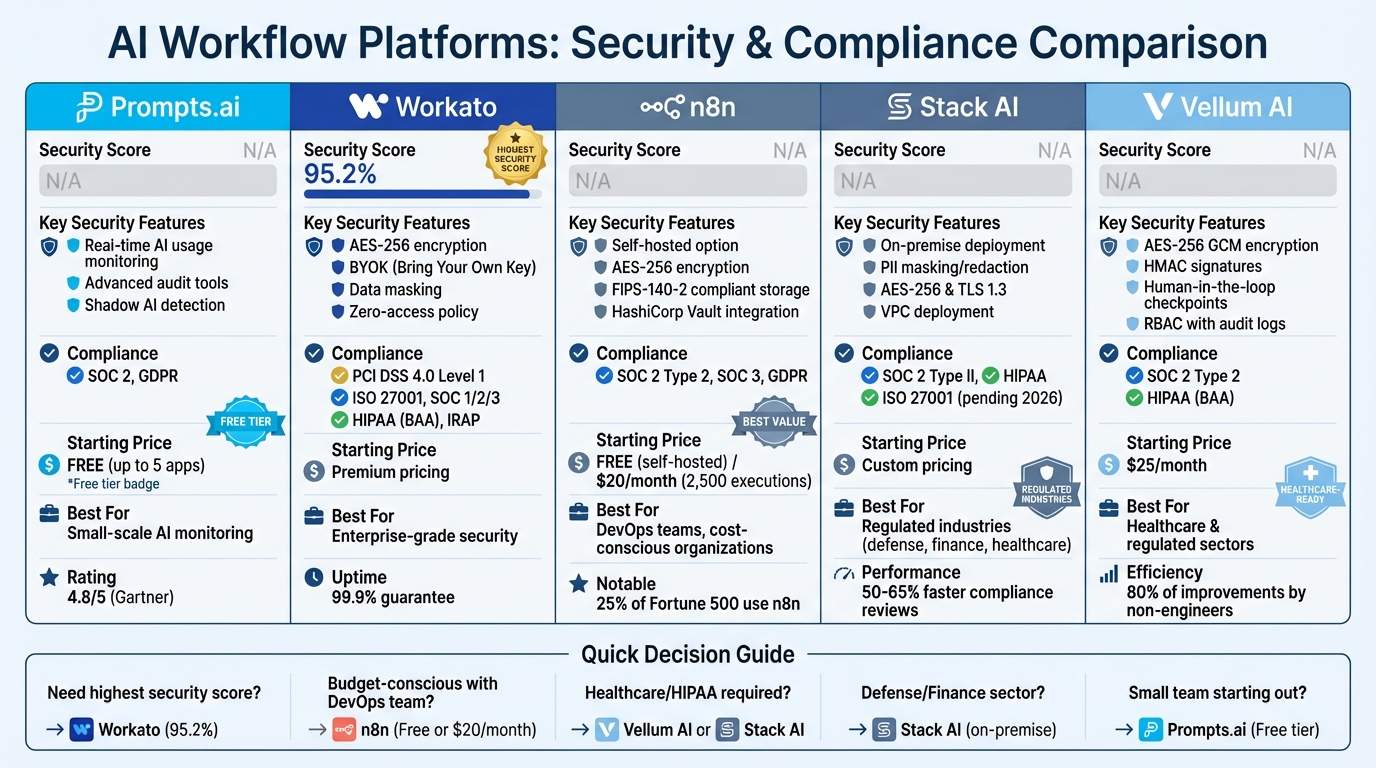
AI Workflow Platforms Security Features and Pricing Comparison
Prompts.ai offers a platform designed to streamline AI orchestration while prioritizing security and governance. It connects with over 35 top-tier large language models, including GPT-5, Claude, LLaMA, and Gemini, ensuring seamless integration while maintaining strict access controls. With Gartner forecasting that over 50% of successful AI-related cybersecurity breaches by 2029 will stem from access control vulnerabilities, safeguarding AI deployments has never been more critical.
Prompts.ai employs a combination of a web browser extension and endpoint sensors to deliver real-time insights into how employees interact with generative AI tools across multiple browsers. This system not only tracks usage patterns as they happen but also uncovers shadow AI applications - those used by employees and embedded in client-facing products. By doing so, it provides security teams with a complete view of potential vulnerabilities within the AI ecosystem.
In addition to its detection capabilities, Prompts.ai offers advanced audit features that enhance organizational oversight.
The platform adopts an audit-first strategy, allowing organizations to observe and understand AI usage patterns before implementing restrictions. This approach fosters trust and ensures effective user training, as highlighted by an industry expert. Through a centralized dashboard, leadership teams can enforce adaptable security measures, manage compliance requirements, and establish detailed policies for third-party AI tools.
Prompts.ai’s governance framework not only strengthens security but also supports scalable enterprise growth through its flexible pricing model.
Prompts.ai uses a usage-based pricing system, where costs are determined by the number of generative AI applications monitored each month. Organizations monitoring up to five apps can start at no cost, while tiered plans are available for larger-scale needs. This model ensures that expenses align directly with usage. As of late 2025, Prompts.ai holds a 4.8/5 rating on Gartner Peer Insights, with 80% of users awarding it five stars. It was also recognized as a 2025 Gartner Cool Vendor in AI Security for its approach to managing AI trust, risk, and security.
Workato provides enterprise-level AI workflow automation, achieving a 95.2% security score from GigaOm Research. The platform ensures data security by encrypting all information using AES-256, both during storage and transmission. Additionally, job history benefits from dual encryption through a global key and a tenant-specific key. To safeguard sensitive information, organizations can enable data masking, which prevents confidential data from appearing in the Workato UI, job history databases, or audit logs.
Workato includes Enterprise Key Management (EKM) with BYOK, allowing businesses to maintain control over their encryption keys. Encryption keys are rotated automatically at an intermediate level every hour, with a cache time-to-live of just five minutes, reducing potential vulnerabilities during workflow execution. The platform enforces a zero-access policy, ensuring that Workato employees cannot access customer recipe job details, data, or execution logs, even during troubleshooting.
Workato is certified as a PCI DSS Level 1 (v4.0.1) service provider, with annual verification by a Qualified Security Assessor. The platform also holds ISO 27001 and ISO 27701 certifications for information security and privacy management, alongside SOC 1, SOC 2 Type II, and SOC 3 attestations. Healthcare organizations benefit from Business Associate Agreements (BAAs) to support HIPAA compliance for handling Protected Health Information. Workato has also completed the Australian IRAP assessment at the "PROTECTED" level and holds NIST 800-171A r2 attestation for managing Controlled Unclassified Information. These certifications integrate seamlessly into its centralized governance framework.
Through AutomationHQ, Workato offers centralized management of multiple workspaces from a single dashboard. The platform employs granular Role-Based Access Control (RBAC) to separate environment roles from project roles, adhering to the principle of least privilege. All user actions and changes are recorded in Activity Audit Logs and Job History Audits, which can be streamed in real-time to external SIEM tools. Passwords for authentication users are rotated every 90 days, and session timeouts can be customized between 15 minutes and 14 days, depending on security needs.
Workato guarantees 99.9% uptime and supports geographic data isolation to meet compliance requirements. For enhanced isolation, businesses can deploy Virtual Private Workato (VPW) within an AWS Virtual Private Cloud. Hans Gustavson, CISO at Workato, emphasized:
"This certification reflects our focus in supporting a secure and scalable orchestration platform that aligns with the evolving needs of our broad base of customers across industries, regions and their size - enterprise, government, startups, SMBs, and beyond."
n8n provides two deployment options: a cloud-based solution hosted on Microsoft Azure in Germany and a self-hosted version, allowing users full control over their data. Around 25% of Fortune 500 companies rely on n8n to create and manage AI workflows, benefiting from its adaptable security framework. The platform ensures data security with AES-256 encryption for stored data and TLS/SSL protocols for data in transit. Its cloud storage encryption follows FIPS-140-2 standards, meeting U.S. federal security guidelines.
n8n's security measures complement its flexible deployment options. It integrates with tools like HashiCorp Vault, AWS Secrets Manager, and Azure Key Vault, enabling secure credential injection into workflows without exposing sensitive information. The platform's cloud infrastructure is safeguarded by Web Application Firewalls (WAF) and Intrusion Detection Systems (IDS), hosted within private networks isolated from public internet access. A built-in security audit tool, accessible via CLI or API, helps identify potential issues such as risky nodes, unused credentials, or missing security settings. Additionally, n8n automatically deletes context data sent to large language models after 30 days and ensures it is never used for model training.
n8n adheres to rigorous compliance standards, maintaining SOC 2 Type 2 and SOC 3 certifications through annual independent audits. It complies with GDPR by offering Data Processing Agreements and Standard Contractual Clauses. While not inherently HIPAA-compliant, n8n supports HIPAA-compliant workflows through self-hosted deployments, where organizations retain full control over their data and can establish Business Associate Agreements with their infrastructure providers. The platform also undergoes third-party vulnerability scans every 90 days and annual penetration tests to reinforce its security posture.
To meet high security standards, n8n includes comprehensive Role-Based Access Control (RBAC) across all paid plans. The Enterprise plan offers advanced authentication options such as Multi-Factor Authentication (MFA), Single Sign-On (SSO), SAML, and LDAP. Audit logs are retained for 12 months, with the most recent three months readily available for analysis. Organizations can also stream workflow events and logs to third-party observability platforms like Datadog or New Relic using webhooks, enabling real-time monitoring of usage, errors, and changes. Dennis Zahrt, Director of Global IT Service Delivery at Delivery Hero, emphasized the platform's impact:
"We have seen drastic efficiency improvements since we started using n8n for user management. It's incredibly powerful, but also simple to use."
n8n has proven its ability to deliver cost savings in practical applications. For instance, Vodafone automated its threat intelligence workflows using n8n, saving approximately $2.9 million. Similarly, Deda.Tech reduced IT Service Management deployment times from two days to just 30 minutes using the platform. n8n offers a free Community Edition for self-hosting, while paid plans provide advanced features. The Enterprise plan is required for capabilities like SSO, SAML, LDAP, and advanced log streaming.
Stack AI combines enterprise-level security with flexible deployment options, making it an excellent choice for highly regulated industries like defense, finance, and healthcare. The platform has achieved SOC 2 Type II compliance for the observation period from March 1 to May 31, 2024, and maintains HIPAA compliance to support healthcare organizations managing Protected Health Information (PHI). Additionally, ISO 27001 certification is underway, with completion expected in early 2026.
Stack AI ensures robust data protection through AES-256 encryption for data at rest and TLS 1.3 for data in transit. Its built-in PII detection feature automatically masks or redacts sensitive information. For organizations with stringent data sovereignty needs, the platform offers on-premise and VPC deployment options, enabling AI agents to operate entirely within a company's private network. AI models are hosted securely using Azure OpenAI and AWS Bedrock, and the platform enforces a strict "no training on user data" policy, backed by Data Processing Addendums.
One notable deployment involved a major U.S. defense contractor using Stack AI’s on-premise solution between 2024 and 2025 to automate Risk Management Framework (RMF) and Authority to Operate (ATO) processes. By keeping all data, inference, and logging within their controlled environment, the contractor achieved a 50–65% improvement in the speed of engineering design compliance reviews, saving hundreds of hours per compliance package. This implementation also enabled the contractor to triple their RFP response capacity without compromising security. This example underscores Stack AI's ability to meet the rigorous demands of regulated industries while maintaining efficiency.
Stack AI goes beyond technical safeguards by providing a detailed governance and auditability framework. Its eight-layer governance model includes RBAC, workspace access, project controls, interface security, global admin policies, connection permissions, production analytics, and authentication. Every change is logged with version history and diffs, creating a clear audit trail. Admins can enforce approval workflows, ensuring users seek review before publishing projects to production, which minimizes the risk of unintended edits.
The platform automatically records every input, output, token usage, and runtime performance, generating audit-ready documentation. Multi-Factor Authentication can be enabled via Settings → Feature Access → Authentication, and Single Sign-On is supported through SAML integrations with providers like Okta and Entra ID. JD Geiger, from Customer Success at Stack AI, highlighted the platform's dedication to security:
"SOC 2 and HIPAA are crucial for fostering robust controls to safeguard customer data. For us, this represents the foundation of a long-term security commitment."
Stack AI’s automation tools provide clear time-saving benefits for regulated industries. Compliance reviews conducted through the platform are 50–65% faster compared to manual engineering design reviews, while AI-assisted proposal drafting reduces drafting time by 60–70%. The platform integrates with over 100 enterprise tools, including SAP, Salesforce, SharePoint, and Workday, allowing organizations to streamline workflows across their existing systems without requiring extensive custom development.
Vellum AI is designed to meet strict regulatory requirements while providing reliable automation for secure AI workflows. The platform boasts SOC 2 Type 2 compliance, verified by Sensiba LLP with a clean audit report, and HIPAA compliance, including Business Associate Agreement (BAA) support for healthcare organizations. These credentials make Vellum a trusted option for industries requiring stringent security standards.
Vellum employs robust security measures to protect user data. It uses AES-256 GCM encryption for data at rest and TLS/HTTPS for data in transit. The centralized Secret Management system encrypts all API keys and service tokens through Google Cloud Platform's Key Management Service (KMS). For organizations prioritizing data privacy, Vellum ensures that interaction data is never shared with LLM providers for training purposes and is only used to fulfill user requests within their accounts. To prevent malicious impersonation, the platform supports HMAC signatures for outgoing API calls. Deployment options include public cloud, private VPC, and on-premise setups, with air-gapped installations available for organizations with strict data residency needs. These security features are backed by a comprehensive governance framework.
Vellum emphasizes transparency and control through its governance framework. It offers Role-Based Access Control (RBAC) for detailed permissions and maintains immutable audit logs to track every action, prompt, and tool call. Enterprises can set data retention policies ranging from 30 to 365 days to comply with regulatory requirements. Built-in versioning for prompts and workflows allows teams to compare versions, identify regressions, and roll back changes instantly. For high-risk tasks, Vellum includes human-in-the-loop checkpoints, pausing execution until a human approver reviews and approves the action, ensuring oversight.
A practical example of Vellum's capabilities comes from Drata, a security and compliance automation platform that adopted Vellum in April 2024. Drata utilized Vellum's Prompt and Workflow products to test AI use cases without risking data security. Pratik Bhat, Senior Product Manager, highlighted the platform's impact:
"We know the power of AI, but how do we make it secure and ensure that we're not compromising privacy and security while still providing value? Vellum has been a big part of accelerating that experimentation part, allowing us to validate that a feature is high-impact and feasible."
Vellum provides a free tier for initial exploration, with paid plans starting at $25 per month. Custom-priced enterprise plans are available for organizations requiring advanced security features, VPC deployments, and dedicated support. Its low-code approach empowers non-engineers to implement nearly 80% of AI improvements, reducing reliance on technical teams. This approach not only speeds up implementation but also ensures that organizations in regulated industries maintain the necessary security controls while achieving faster results.
The strengths and limitations of these platforms reflect their commitment to rigorous security and compliance measures while balancing operational efficiency. Each option caters to different organizational needs, offering unique features and trade-offs.
Workato excels with a 95.2% data security score from GigaOm Research and a 99.9% uptime guarantee, meeting PCI DSS 4.0 Level 1 standards. Its Virtual Private Workato (VPW) and Bring Your Own Key (BYOK) encryption provide organizations with full control over encryption keys. However, these premium features may not be cost-effective for smaller teams.
n8n stands out for cost-conscious users, offering a free self-hosting option and execution-based pricing starting at $20 per month for 2,500 executions. While self-hosting provides complete infrastructure control, it requires dedicated DevOps expertise, which may be a hurdle for some organizations.
Vellum AI caters to regulated industries with SOC 2 and HIPAA compliance, starting at $25 per month. While its compliance capabilities are well-suited for sectors like healthcare and finance, organizations needing advanced security features might face additional costs for enterprise-level solutions.
Here’s a quick comparison table summarizing the key aspects of each platform:
| Platform | Security Strengths | Compliance Certifications | Governance Highlights | Cost Efficiency | Limitations |
|---|---|---|---|---|---|
| Workato | VPW instances, BYOK with hourly key rotation, data masking | PCI DSS 4.0 Level 1, ISO 27001, SOC 1/2/3, IRAP | AutomationHQ federation, SCIM provisioning, real-time SIEM log streaming | Premium pricing for enterprise features | High cost barrier for smaller teams |
| n8n | Self-hosted control over infrastructure | Varies by self-hosted setup | Detailed in platform overview | Free self-hosting; $20/month for 2,500 executions | Requires in-house DevOps expertise |
| Vellum AI | Enterprise-grade security measures | SOC 2, HIPAA | Detailed in platform overview | Entry pricing at $25/month | Additional costs for advanced features |
For industries like finance and healthcare, platforms with verified compliance certifications are critical. Workato's PCI DSS Level 1 certification and Vellum AI's HIPAA compliance offer the assurances needed for audit trails and regulatory requirements. Teams prioritizing data privacy may lean toward n8n's self-hosted solution, which keeps workflow code entirely within internal infrastructure. However, this approach necessitates technical expertise and ongoing maintenance.
Choosing the right platform requires balancing security, compliance, and operational needs to ensure long-term success.
Choosing the right AI workflow platform means aligning your organization's security priorities with the necessary certifications, features, and operational structure. For enterprises in regulated industries, Workato's Virtual Private Workato instances and BYOK encryption offer strong isolation and compliance measures. That said, its higher pricing might pose challenges for organizations with tighter budgets.
On the other hand, n8n's self-hosted model provides complete control over data residency and security, making it an excellent choice for teams that can allocate DevOps resources. Its cost-effectiveness is evident - Vodafone, for instance, saved approximately $2.9 million by leveraging n8n for critical workflows[2].
Ultimately, the decision rests on your organization's specific compliance requirements, technical capabilities, and budget constraints. Whether you prioritize certified platforms or the adaptability of self-hosted options, the ideal solution will strike the right balance between security, compliance, and operational efficiency to support your organization's objectives.
Key measures to secure AI workflows include encryption for both data at rest and in transit, role-based access control (RBAC) to restrict access to authorized users, and continuous monitoring to identify threats in real time. Other critical safeguards include maintaining audit logs, adhering to regulations like GDPR and HIPAA, and implementing secure identity management methods, such as single sign-on (SSO) and multi-factor authentication. These steps help protect sensitive data, maintain system integrity, and ensure compliance with legal requirements.
When choosing between cloud, VPC, and on-prem deployments, it's important to weigh your organization's needs for control, security, and compliance.
For flexibility, hybrid models can blend these approaches to address specific operational and compliance needs.
To maintain secure and compliant AI workflows, focus on audit logs that document workflow actions, access, and any changes made. Look for governance features such as role-based permissions, encryption, and adherence to standards like SOC 2, GDPR, and HIPAA. Additionally, tools for monitoring data security and ensuring regulatory compliance are essential components of a reliable system.


