
AI adoption is transforming businesses, but it comes with new security risks like data breaches, compliance challenges, and emerging threats such as prompt injection and model poisoning. To protect sensitive data and ensure regulatory compliance, businesses need robust AI security solutions. Here’s a quick look at five leading providers addressing these challenges:
Each platform provides unique strengths, from runtime monitoring to cost management, ensuring businesses can secure their AI workflows effectively. Below, we explore their features and how they address the industry's most pressing AI security concerns.
Prompts.ai takes a proactive approach to AI security by embedding protection directly into the development process, rather than treating it as an afterthought. Handling over 10 billion tokens daily with a 99.99% uptime SLA, it proves that top-tier security can coexist with exceptional performance and reliability.
The platform offers real-time threat detection, capable of identifying and blocking prompt injection attacks, adversarial inputs, and unauthorized data exposure as they happen. Automated PII redaction ensures that sensitive information, such as customer data, employee records, and proprietary details, remains secure without requiring manual oversight.
Adding security is quick and straightforward - less than 3 minutes with just 3 lines of code using a lightweight SDK. No changes to existing infrastructure are needed, and the platform works effortlessly with any LLM provider through a unified API supporting over 1,600 models. With built-in support for Node.js, Python, and cURL, developers can implement robust security using tools they already know, without having to navigate new frameworks or manage multiple SDKs.
"Stop choosing between speed and security. Our platform gives you both with enterprise-grade protection that integrates in minutes." - Prompt Shields
Prompts.ai provides a full audit trail, tracking every AI interaction, including the models accessed and the prompts submitted. Centralized authentication and policy management ensure that outputs align with regulatory requirements. Features like version control and A/B testing allow teams to document prompt changes and their effects, creating the detailed records regulators demand.
The platform's real-time observability dashboards give teams a clear view of LLM behavior, costs, and guardrail violations across the AI stack. This transparency helps identify anomalies, flag prompts that trigger security rules, and analyze how models handle sensitive data, turning opaque AI operations into traceable and auditable processes.
Prompts.ai employs dynamic model routing and semantic caching to cut costs by 40% through smarter request management. It automatically switches between models during failures or errors, ensuring uninterrupted uptime while keeping expenses in check. Detailed usage analytics connect token consumption to specific teams, projects, and use cases, making it easier to pinpoint inefficiencies and adjust spending without sacrificing security.
Check Point Infinity AI strengthens security with a Zero Trust framework, treating every interaction as potentially risky. This approach is particularly effective for businesses managing hybrid environments that blend cloud services, on-premises systems, and remote teams - situations where traditional perimeter defenses often fall short.
At the heart of the platform is ThreatCloud AI, an advanced intelligence engine that leverages data from over 50 AI engines and millions of sensors to block threats in real time. It boasts an impressive 99.8% block rate for malware and phishing, thwarting over 3 billion attacks annually. Threat intelligence updates across the security stack in under two seconds, ensuring swift and comprehensive protection. The Infinity GenAI Protect module adds another layer of defense, safeguarding sensitive information as businesses adopt Generative AI. This is critical, as 76% of security leaders identify data leakage as their top concern.
Building on its real-time threat prevention, the platform also enforces strict compliance measures. The Quantum Policy Auditor simplifies audits by reviewing thousands of rules instantly and translating technical policies into clear, visual insights for audit teams. The AI Security Posture Management (AI-SPM) framework continuously monitors AI ecosystems, identifying policy violations and governance gaps. Additionally, Infinity GenAI Protect provides a unified audit trail, logging risky user activities in detail to meet regulatory requirements. These tools help businesses manage compliance risks while integrating AI platforms.
The Infinity Portal consolidates security controls into a single management interface, enforcing policies for over 10,000 applications. It also integrates seamlessly into CI/CD pipelines, ensuring smooth operations. Through Infinity Playblocks, the platform automates workflows across third-party security tools, eliminating the need for custom scripts or manual intervention. This streamlined integration enables dynamic adjustments to defenses in real time.
The Infinity AI Copilot acts as a virtual assistant, proactively recommending updates to data loss prevention (DLP) rules and firewall settings based on emerging vulnerabilities. By automating routine tasks, it reduces task resolution times by up to 90%. This ensures strong security while protecting sensitive data throughout the AI adoption process. As Milinko Milincic, Director of Technology and Information Security Architect at Fast Pace Health, noted:
"With Infinity XDR and Playblocks we are able to see attacks in real-time and it's given us the ability to stop attacks in their tracks. It shortens our time to respond significantly."
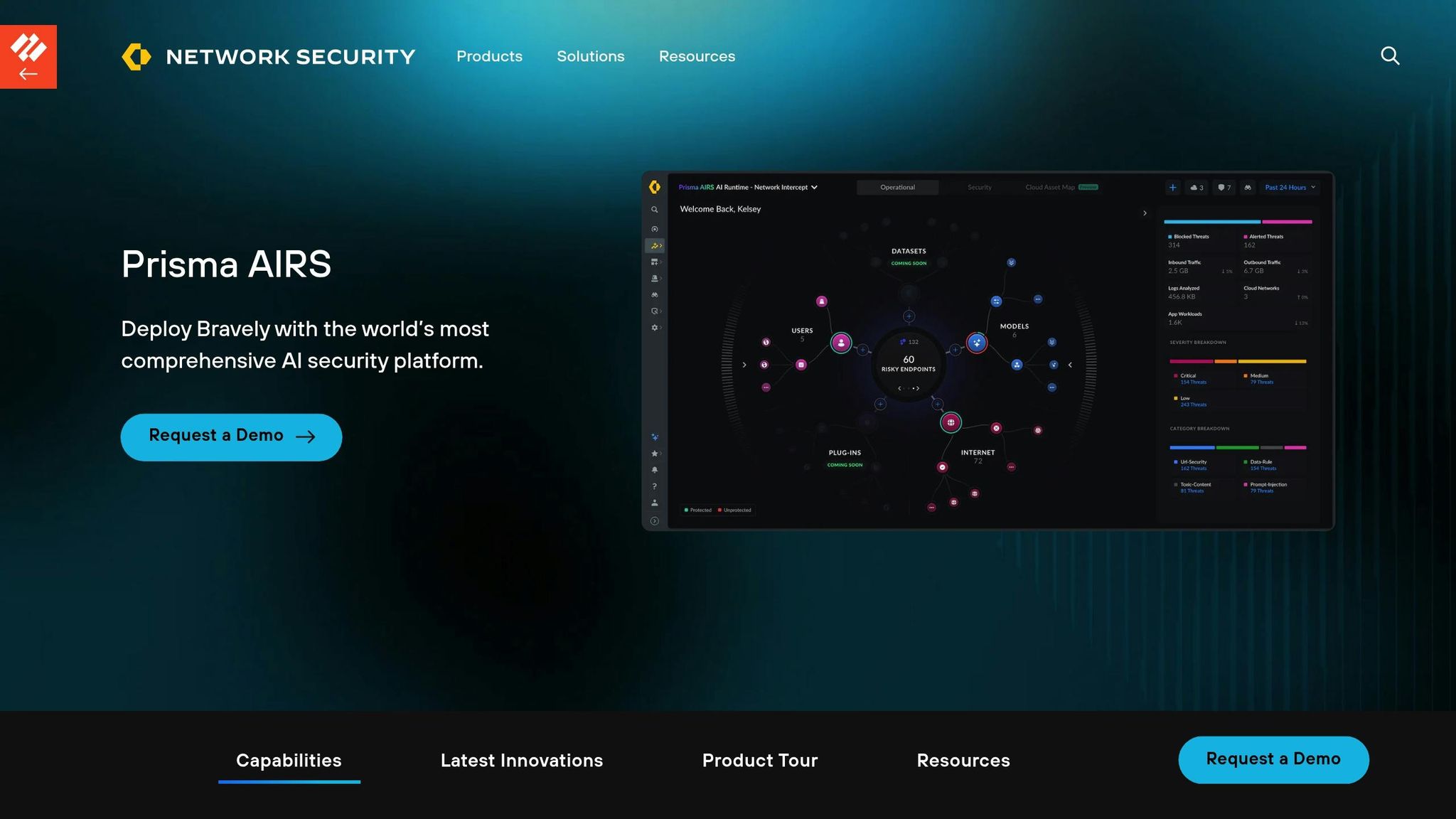
Palo Alto Networks Prisma AIRS stands out as a secure AI platform designed to integrate security measures at every stage of development. With an API-first approach, it scans millions of models and identifies over 25 different threat patterns across more than 20 model formats.
The AI Runtime Firewall plays a critical role in defending against threats like prompt injection, malicious code, and denial-of-service attacks. It thoroughly inspects both inputs and outputs from AI models to detect sensitive data, such as personally identifiable information (PII) and intellectual property. By integrating with Enterprise Data Loss Prevention (DLP), Prisma AIRS ensures sensitive information stays within organizational boundaries. Sunil Agrawal, CISO at Glean, highlighted its strengths:
"What makes Palo Alto Networks AI Runtime stand out are three things. It has three functionalities - built-in data security, malware security and AI security."
Additionally, the AI Agent Security module provides continuous monitoring to prevent identity fraud and misuse, safeguarding AI agents that handle sensitive systems and data.
Prisma AIRS offers AI Posture Management, which identifies misconfigurations, excessive permissions, and risky trust chains within AI infrastructure. The AI Red Teaming feature conducts over 500 adversarial simulations to uncover vulnerabilities, mapping results to key security frameworks. This automated process ensures that models meet both internal standards and external regulatory requirements before deployment. The platform generates reports tailored for both executives and operators, offering actionable guidance to resolve risks quickly. Full audit trails of AI agent interactions further enhance accountability and transparency during regulatory reviews.
The platform's API-first design makes compliance processes more efficient and straightforward to implement.
Prisma AIRS integrates seamlessly into existing development workflows, thanks to its Security-as-Code approach. Developers can embed security directly into source code using REST APIs and a Python SDK. This design works effortlessly with CI/CD and MLOps pipelines, allowing for programmatic scanning of prompts and model responses without disrupting operations. Organizations already using Palo Alto Networks VM-Series virtual firewalls can upgrade natively, avoiding the need for major infrastructure changes. Deployment is simplified with Terraform templates for AWS and Azure, along with "Auto-Execute" features for rapid firewall deployment via Strata Cloud Manager. Native integrations with tools like Microsoft Foundry, Glean, and Portkey further enhance the platform's ability to secure AI agents in existing environments.
The AI Runtime Firewall has the capacity to handle up to 10,000 AI transactions daily per vCPU, monitoring network traffic for malicious URLs and suspicious activity. Steve Jablonski, CISO at TELUS Digital, shared his perspective:
"What we're excited to see is the ability for us to now look and see how API calls are being made. We can look at malicious detections that are being performed by agent AI tools across the board."
This model-agnostic platform is compatible with any AI model architecture or framework, ensuring consistent security across a variety of AI environments. Continuous monitoring helps detect threats like data poisoning and adversarial inputs before they can compromise model integrity.
Prisma AIRS introduces flexibility in cost management with its Software NGFW Credits (Flex Credits) system. This allows businesses to reallocate existing security investments to cover AI workloads. Starting February 2026, token-based licensing for the AI Runtime API will provide more granular, usage-based pricing. To aid in budget planning, the platform includes a Credit Estimator tool, helping organizations predict credit requirements and avoid unexpected expenses as AI adoption grows.
Lasso Security acts as a highly efficient gateway between AI applications and users, inspecting every interaction in real time. It offers a 570x cost advantage over cloud-native alternatives, achieves 99.8% accuracy in detecting content, context, and intent, and delivers classification speeds under 50ms. This ensures real-time protection without noticeable delays, effectively addressing modern AI vulnerabilities while keeping performance intact. Additionally, the platform's advanced data protection measures stand out as a key component of its approach.
Lasso takes a proactive stance with its Intent Security system, which goes beyond simple pattern recognition by analyzing user intent. This enables it to identify sophisticated malicious actions, like payload splitting and obfuscation, that can bypass traditional filters. When threats are detected, the platform automatically applies data masking and redaction to safeguard personally identifiable information (PII) and protected health information (PHI).
The Context-Based Access Control (CBAC) feature dynamically adjusts access to sensitive data based on user roles, query intent, and data classification, rather than relying on static rules. Lasso also tackles the issue of "Shadow AI" - unauthorized AI tools used by employees without proper security checks. According to Lasso's data, over 13% of employees share sensitive information with generative AI applications, making this discovery feature particularly critical.
Lasso supports compliance with major regulatory frameworks, including the EU AI Act, GDPR, NIST AI Risk Management Framework, ISO/IEC 42001, and the U.S. Executive Order on AI. Its Intent Deputy feature simplifies compliance reporting by using an 8-dimensional coordinate system to provide clear, explainable evidence of compliance, achieving 99.83% detection accuracy. Itzik Menashe, CISO & VP IT Productivity, highlighted the platform’s dual benefits:
"Lasso's investigative tools have been incredibly valuable. But they also help to prevent risks proactively by educating our employees about responsible AI usage. This has been key to enabling innovation while maintaining compliance and security."
For healthcare organizations, the platform automatically detects PHI or patient outcomes during AI interactions, generalizing or redacting sensitive language to ensure compliance. In financial services, its context-sensitive enforcement ensures that analysts access detailed revenue data, while customer success managers receive only aggregated summaries suited to their roles. These robust compliance measures naturally lead into Lasso's seamless integration options.
Lasso offers flexible deployment options, including Gateway, API, or SDK. It integrates smoothly with existing enterprise security tools like SIEM, SOAR, ticketing systems, and messaging platforms. The platform’s custom policy wizard simplifies policy creation with plain language commands, eliminating the need for complex coding. Additionally, a library of pre-built policies accelerates deployment. Gil Ohayon, CIO, praised the platform’s control features:
"Lasso's full security suite has been crucial in fortifying our GenAI applications. Their approach ensures our organization, customers, data, and employees stay protected from various attacks while allowing me full control over my environment."
Lasso ensures continuous monitoring of large language model (LLM) data transfer interactions, with autonomous response actions that reduce the need for manual intervention. Using 3,000+ attack simulations, its offensive AI agents test system resilience against threats like prompt injection, agent goal hijacking, and tool abuse, identifying vulnerabilities before they can cause harm. The platform treats all model outputs as untrusted, recognizing that LLMs can inadvertently leak sensitive data even when inputs appear safe. This constant oversight enables organizations to adopt AI securely while maintaining operational integrity.
Zscaler combines zero trust principles with real-time monitoring to create a unified solution for securing AI environments. Operating on the Zero Trust Exchange, the platform processes 5 trillion daily signals to safeguard rapidly growing AI traffic. Between 2024 and 2025, enterprise AI/ML application traffic surged by an astonishing 3,464.6%, yet organizations blocked nearly 59.9% of AI/ML transactions due to concerns about security and governance. This explosion in adoption highlights the urgent need for tools that enable secure AI implementation.
Zscaler employs inline Data Loss Prevention (DLP) with over 100 specialized dictionaries to scan AI prompts and responses in real time for sensitive data such as Source Code, PII, PCI, and PHI. The platform also uses browser isolation to contain AI applications in dedicated sessions, restricting clipboard actions like copy, paste, and downloads to prevent data leaks. Jason Koler, CISO at Eaton Corporation, which oversees 90,000 users across 170 countries, shared his experience with Zscaler in early 2024:
"We had no visibility into [ChatGPT]. Zscaler was our key solution initially to help us understand who were going to it, what were they uploading, and then providing awareness."
The platform automatically identifies and secures thousands of embedded AI applications within SaaS platforms, centralizing their management. It integrates Zero Trust access with features like single sign-on (SSO), multi-factor authentication (MFA), and comprehensive TLS/SSL inspection, ensuring only authorized users can access approved AI tools. Additionally, the AI Guard feature moderates prompts and responses in real time, blocking prompt injections, jailbreaks, and harmful content.
These measures align seamlessly with Zscaler's broader strategy for ensuring secure and compliant AI adoption.
Zscaler supports compliance with frameworks such as NIST AI RMF, HIPAA, CJIS, PCI DSS, and CCPA while logging all interactions for forensic analysis. Leveraging technology from its SPLX acquisition, the platform's automated red teaming conducts over 5,000 simulated attacks across various scenarios to identify vulnerabilities before deployment. Eric Andrews, VP of Product Marketing - Data Security at Zscaler, explained:
"Zscaler's AI security portfolio also addresses governance and compliance, with built-in frameworks for EU AI Act, NIST AI RMF, OWASP Top 10 and other popular regulations. This enables organizations to quickly test and assess for compliance and remediate any gaps."
Zscaler research found that improper generative AI use without Zero Trust protections led to a 47% increase in compliance violations across industries in 2025. The platform's Policy Generator uses red teaming insights to automatically create and enforce guardrail policies. For Microsoft Copilot users, Zscaler manages OneDrive data permissions, ensuring excess access is revoked to prevent misconfigurations and oversharing.
Zscaler’s Zero Trust Exchange eliminates the need for multiple point products by offering a unified platform with deep integrations into major AI ecosystems, including OpenAI, Anthropic, AWS, Microsoft, and Google. Its inline architecture inspects AI traffic, including protocols like MCP (Model Context Protocol) and websockets. Zeus Kerravala, Principal Analyst at ZK Research, highlighted the platform’s importance:
"What's important here isn't just another security tool; it's the shift toward a Zero Trust framework that actually understands the context of an AI conversation. Without this level of deep inspection and automated guardrails, enterprises are essentially flying blind."
The platform automatically detects and classifies thousands of AI applications, including those embedded in SaaS platforms like Salesforce and Atlassian, bringing them under centralized security management. It also ensures secure, zero trust access to AI development environments and IDEs, allowing developers to connect to AI infrastructure while preventing PII leaks. The AI Asset Management feature provides a detailed inventory and dependency map of an organization’s AI ecosystem, covering models, agents, and infrastructure.
With this unified security framework, Zscaler continuously monitors AI interactions to address threats as they emerge.
Zscaler ensures ongoing protection by maintaining continuous risk assessments from the build phase through runtime. Its AI Guard solution, available for general use, blocks malicious attacks in real time. Research shows enterprise AI systems can be compromised in just 16 minutes, with critical vulnerabilities found in all systems analyzed. The platform’s prompt extraction and classification capabilities provide insights into usage patterns while preventing data leaks during active AI interactions. It also addresses emerging communication protocols, such as Agent-to-Agent (A2A), ensuring robust protection in evolving AI environments.

Comparison of Top 5 AI Security Platform Features and Capabilities
Each provider offers distinct benefits in the realm of AI security, but no solution is without its limitations. Understanding these strengths and gaps is essential for aligning their capabilities with your organization's specific goals.
Here’s a closer look at what each provider brings to the table:
Prompts.ai stands out by centralizing 35+ AI models under a unified governance framework while maintaining enterprise-grade security. It simplifies operations and provides real-time financial insights for every AI interaction. However, its recent acquisition of SentinelOne raises questions about how quickly integration will be completed.
Check Point Infinity AI has strengthened its AI threat defense capabilities through its September 2025 acquisition of Lakera, which enhanced its ability to integrate prompt firewalls into existing systems. Despite these strengths, the platform may fall short in offering full visibility into critical cloud assets, such as exposed notebooks or unencrypted training buckets.
Palo Alto Networks Prisma AIRS expanded its security stack with the Protect AI acquisition in April 2025, becoming a leader in integrating specialized AI security into its platform. Its comprehensive approach covers multiple layers of the AI stack, but organizations relying on multiple point solutions might encounter challenges with integration and operational efficiency.
Lasso Security takes a focused approach, concentrating exclusively on AI security. This specialization brings deep expertise in AI-specific threats. However, the platform often emphasizes observability over enforcement, leaving organizations needing additional tools to translate governance policies into active runtime controls.
These evaluations highlight the diverse strategies within the industry. A broader trend also emerges: 76% of security leaders identify data leakage as the top risk associated with Generative AI. Yet, many tools fail to address critical areas like runtime enforcement, infrastructure gaps, and data sovereignty. For organizations managing AI risks, a layered defense strategy is essential. Deciding between an integrated platform and specialized solutions depends heavily on your current security setup and risk tolerance.
When selecting an AI security solution, it’s crucial to align your organization’s priorities with the specific strengths of each platform. Start by identifying whether your focus is on unified governance, fast threat detection, or streamlined security consolidation.
For industries that require stringent data protection during processing, look for platforms offering Confidential Computing to encrypt data while it’s actively being used - this is especially vital for regulated sectors. If Shadow AI is a concern, prioritize solutions with detection capabilities that achieve up to 95% accuracy, far exceeding the 5–25% range of traditional pattern-matching approaches.
Speed and scalability are also essential. API-first platforms with latency under 10 milliseconds can handle billions of requests without compromising user experience. Additionally, solutions with robust native integrations and advanced tools - like field-level tokenization and automated compliance mapping for standards such as ISO, NIST, and GDPR - can save time and resources.
AI-native security platforms also deliver measurable ROI, automating up to 80% of incident remediation. Choose a solution that strengthens your AI workflows while addressing your compliance, cost, and performance goals.
Key risks in AI security demand attention, particularly in areas like data protection weaknesses, model-specific threats, and compliance shortcomings. Attackers often exploit vulnerabilities such as inadequate authentication measures or flaws in public-facing applications. Strengthening access controls, implementing robust encryption, and deploying real-time threat detection systems are critical steps to mitigate these risks. Additionally, challenges like model theft and prompt injection require proactive strategies, including runtime security measures and ongoing monitoring, to protect both sensitive data and AI systems effectively.
To safeguard prompts and responses while keeping app performance intact, consider using specialized AI security tools built to minimize latency. These tools effectively counter threats such as prompt injection and data exfiltration without slowing down operations. Additionally, embedding security features directly into AI orchestration platforms allows for secure workflow management. Incorporating lightweight, real-time threat detection modules further enhances protection by preventing attacks efficiently, all while maintaining responsiveness.
To ensure AI compliance during audits, it’s essential to maintain thorough documentation of governance policies, detailed audit trails, and real-time monitoring systems. Adherence to established standards such as SOC 2, GDPR, and HIPAA is critical. Additionally, implementing continuous risk assessments and leveraging automated controls can help address compliance needs efficiently and proactively.


